CedeDrive product overview - see it in action now
CedeDrive is complete data security without compromising your way of working. Whether we are aware of it or not, all of our data is stored on drives, whether it is hard drives, external drives, flash drives, or network drives. One of the main concerns today is what happens to this data when a drive is lost or stolen.
CedeDrive eliminates this concern by providing a military strength encryption layer between your valuable data, and the drive it is stored on. CedeDrive does not compromise your way of working, and no additional steps are required to ensure your data is encrypted. One of the best features of CedeDrive is that you will forget it is there, whilst it silently secures your data as you work.
CedeDrive not only protects the data on your laptop or desktop, it will also secure the data on all of your portable storage devices. These include external hard drives, USB flash drives and even network drives.
Convert USB Flash Drives & Portable Hard Drives
One of the great features of CedeDrive is the ability to instantly convert any standard USB Flash Drive into an Encrypted Flash Drive, functioning exactly like a hardware encrypted flash drive. There is no need to buy additional hardware encrypted devices. The additional benefit is you can also convert portable USB hard disks of any size. You can then use your converted flash drive in any other computer without installing additional software on that computer.
Conversion of Flash Drives and Portable Hard Drives is accomplished in a 1 click process that will also preserve all of your existing data on your flash drive or portable hard disk. Your data is automatically backed up, your flash drive converted and then all of your data is restored to the encrypted flash drive.
Complete transparency
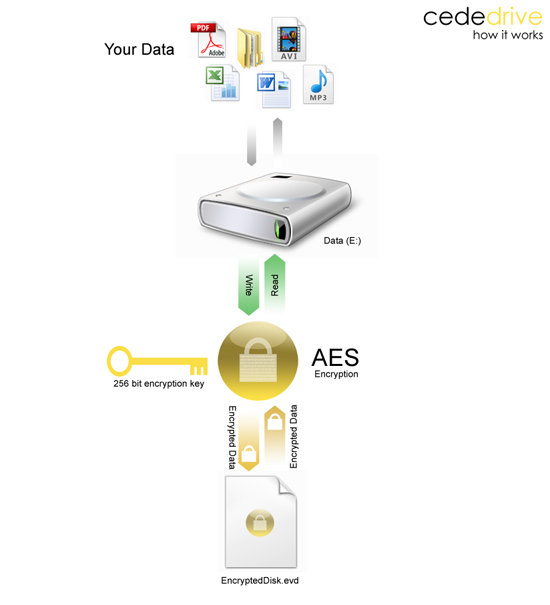
CedeDrive uses on-the-fly virtual drive technology. A virtual drive acts exactly like a normal drive such as your C:\ drive, apart from it is actually writing and reading from a protected file on any location you choose. CedeDrive uses AES 256-bit military grade encryption technology to secure your valuable data.
CedeDrive launches automatically when you log onto your computer, and asks you for a single password. After your password is verified all of your encrypted drives are automatically activated instantly and you can start accessing them straight away. CedeDrive is fast, there is no waiting for data to decrypt or encrypt, it is all done using high performance encryption algorithms allowing you to work with your data whilst forgetting that CedeDrive is securing your data silently.
There are also no limits to the size of a Cede Drive. You can create encrypted drives of any size on any hard disk and even USB flash drives.
Robust Security
Once secured by CedeDrive's powerful encryption standard, sensitive files and folders are stored safely on your laptop, desktop and all of your portable devices. Working on encrypted files is as easy as entering one single password, and all of your encrypted drives will be mounted automatically ready for you to use just as you would use any USB flash drive or external hard drive. There are no additional steps necessary to encrypt or decrypt your data. It's so easy, you'll forget you have it installed.
Easy To Deploy Across Organisations
CedeDrive is competitively priced and installs in seconds, requiring little disk space or memory. Because of its ease of use and small footprint, it does not interfere with the working environment or employee performance. Available as an instant download and with a distribution wizard for large organisations, CedeDrive is your last line of defence without compromising performance, but more importantly your time.
Powerful Encryption Technology
The encryption used by CedeDrive cannot be broken. CedeDrive does not store any encryption keys anywhere on your computer, not even in memory. Therefore should your computer fall into the wrong hands, you can be sure that nobody apart from you can gain access to a drive secured with CedeDrive. CedeDrive is extremely efficient and does not use up valuable resources, such as memory and cpu time.
|
|
|
Completely transparent, no additional steps needed to encrypt or decrypt
User experience unchanged
Regulatory compliance
Military strength AES-256 bit Encryption
Cryptography FIPS 140-2 certified
Turns existing flash drives into encrypted drives removing the need for expensive upgrades
|
|
|
|